Who is Your Trusted IT Advisor?
We act as a trusted IT advisor for many of our clients. What does that mean exactly?
Most business owners understand the importance of including their accountant and lawyer in any business changes that have legal or tax implications. It is very important to ensure that the right structures are in place to minimise tax, meet legal obligations and ensure that liability and risk are minimised and managed.
It is equally important to seek the advice of a Trusted IT Advisor in the same instances. A Trusted IT Advisor sits on your side of the table, seeks to understand your business and can then make suggestions that are your in best interest. Here are some of the many reasons why this is important.
- Adding or terminating staff or employees should be done correctly. Ensuring they have the right hardware, software and access to corporate systems and data before they start work eliminates up front teething problems and gets them up to speed right away. Ensuring an employee’s access is removed BEFORE terminating reduces the risk of data theft and malicious behaviour.
- Technology can be configured many different ways, and what could be right for one scenario might not be right for another.
- Starting a new business, opening a new store, or even just working from home might require different security, backup solutions and data storage solutions. It is best to define these and understand the cost of implementation before the decision is made.
- Technology replacement plans should be in place to cycle hardware every few years. These may need to be modified if changes in ownership, downsizing or scaling up are planned.
So before you make important business decisions, contact us for a no obligation free chat. We would love to be your Trusted IT Advisor.
Kochie takes a Small Business through a Technology Makeover
David Koch from Channel 7 presented a small business makeover series with Microsoft last year. The 4 part series takes approximately 40 minutes to watch and is well worth the time taken.
If your business can relate to any of the problems presented here, or would like any of the solutions then please call us. This is what we do! Using technology correctly can improve workers productivity and business efficiency. Being able to do things for your customers your competitors can’t do may just give you the edge!
Talk to us about improving your Business Productivity and Efficiency with New Technology, Software, mobile access and better workflows
Windows 10 – Latest Version
Are you running the latest version of Windows 10 yet?
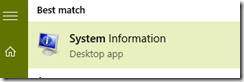
You can work it out by hitting the start button and typing System and clicking System Information.
In the OS Version you should see 10.0.10586 Build 10586. If not, you are running an older version.
You can update by running Windows updates and ensuring it downloads this new version.
Note: Check with us if you are not sure, or want support to running this version update.
And if you are running Windows 7 or 8 then time to upgrade – you have 3 months left for the free upgrade.
Book us in to upgrade your business or Home PCS to Windows 10 now – $150 per machine. conditions apply.
Security and Computing
Security is an ongoing battle of threats and defence. The cost to businesses to remove malware and viruses is a lot more than the small cost of educating yourself and taking appropriate defensive measures.
Are you up to date with the latest threats?
Three types of malware you should know about in 2016 Have you heard of the Brain Test, Zeus or Conficker threats? Are you safe? Read this article to learn more.
Who is most at risk of identity theft? You might be surprised to find out just who is more at risk of identity theft. Read this article to learn more. Or read our previous articles about protecting yourself and your business’s data.
Are you at risk from Spear Phishing attacks? Do you know how to recognise them and keep safe from them? There are many ways the attacks can come but the most popular delivery platform is email. As such, when opening an email it is important to know the hallmarks of a phishing scam:
- If it asks for your personal information, play it safe and assume it is a phishing attack.
- If you believe the email may be a scam, phone the organisation to verify if it is an official email.
- If you do click on a link, make sure to never enter your information into the website that appears.
- If you recognise the email address, do not take this as proof it is from an official or authentic source.
- If you see a suspect email has an attachment, make sure you do not open or download it as it could be an infectious computer virus.
Be safe and secure online – ask us how if you need to know more
Follow Us On Social Media
As always Jethro is your web, cloud and technology specialists. I am constantly learning new things and spending time researching, playing and testing new systems and reading about other people in the IT world doing the same thing. If you want to follow along with what I share in various spaces, then connect with me:
- Twitter https://twitter.com/spyjournal technology, cycling, social media, management, business, and web
- Linked In http://www.linkedin.com/in/jethromanagement
- Delicious https://delicious.com/jethrocon saved links
- Blog http://spyjournal.biz all sorts of stuff including personal and family updates
- Spyjournal Facebook https://www.facebook.com/spyjournal.biz tech, cycling, and other stuff
- Subscribe to our daily Newspaper https://paper.li/spyjournal/1345852972
- Subscribe to our weekly Newspaper https://paper.li/spyjournal/1345853288
- Jethro Management Facebook https://www.facebook.com/JethroManagement business, management, web
- Jethro Marketing Facebook https://www.facebook.com/JethroMarketing social media, marketing
- Dreamcoat Photography Facebook https://www.facebook.com/DreamcoatPhotography
- Dreamsport Photography Facebook https://www.facebook.com/DreamSportPhotography
- Red Hot Snapper Facebook https://www.facebook.com/redhotsnapper roller derby